Palo Alto Networks
GlobalProtect

GlobalProtect extends the same next-generation firewall-based policies that are enforced within the physical perimeter to all users, no matter where they are located. In effect, GlobalProtect establishes a logical perimeter that extends policy beyond the physical perimeter. Employees working from home, on the road for business, or logging in from a coffee shop will be protected by the logical perimeter in the same manner that they would be if they were working from their office.
GlobalProtect Agent
The GlobalProtect agent is a small piece of software that resides on the end-user’s PC (Mac too). This agent can be delivered to the user automatically via Active Directory, SMS or Microsoft System Configuration Manager or can be downloaded directly from the GlobalProtect Portal. The agent does three key things: It communicates to the GlobalProtect Portal to obtain the appropriate policy for the user. It establishes and maintains a secured connection to the nearest (fastest) Palo Alto Networks GlobalProtect Gateway. And lastly it compiles a Host Information Profile (HIP) of the client device including such factors as patch level, disk encryption, antivirus version and many more.
GlobalProtect Portal
The GlobalProtect Portal provides the centralized management for the solution. Any Palo Alto Networks firewall can act as the portal while also performing its everyday duties as a next-generation firewall. However, each GlobalProtect deployment will only have 1 portal at a time. The portal provides three key functions:
- It delivers the GlobalProtect Agent to users.
- It provides the GlobalProtect agents with a list of available GlobalProtect Gateways.
- It manages the authentication certificates for the solution.
The GlobalProtect Portal, like all Palo Alto Networks can be run as a high-availability pair, to ensure always-on reliability of the solution.
- It delivers the GlobalProtect Agent to users.
- It provides the GlobalProtect agents with a list of available GlobalProtect Gateways.
- It manages the authentication certificates for the solution.
The GlobalProtect Portal, like all Palo Alto Networks can be run as a high-availability pair, to ensure always-on reliability of the solution.
NOTE: Starting with PANOS 7.0, you no longer need to purchase the GP Portal License.!
GlobalProtect Gateway
The GlobalProtect Gateways are responsible for the majority of the actual security enforcement in the solution. Similar to the portal, any Palo Alto Networks firewall can be a gateway for the GlobalProtect solution. However, unlike the portal, you can leverage as many gateways simultaneously as you need, ensuring multiple potential routes between an agent and gateway. The Gateway has three core functions: First and foremost, it performs the full breadth of next-generation firewalling functionality including application control, threat prevention, URL filtering, user visibility, etc on all traffic from associated GlobalProtect Agents. It also provides the end of the secure connection established by the Agent. Lastly, it receives the Host Information Profile (HIP) and enforces policies accordingly.
Global Protect capabilities by PAN firewall platform
GlobalProtect Client VPN
| Firewall Model | Max tunnels (SSL, IPSec, and IKE with XAUTH) |
|---|---|
| PA-5280 | 60,000 |
| PA-5260 | 60,000 |
| PA-5250 | 30,000 |
| PA-5220 | 15,000 |
| PA-3260 | 2,048 |
| PA-3250 | 2,048 |
| PA-3220 | 1,024 |
| PA-850 | 1,000 |
| PA-820 | 1,000 |
| PA-460 | 1,500 |
| PA-450 | 1,500 |
| PA-440 | 1,000 |
| PA-220 | 250 |
| VM-700 | 12,000 |
| VM-500 | 6,000 |
| VM-300 | 2,000 |
| VM-200 | 500 |
| VM-100 | 500 |
| VM-50 | 250 |
| VM-1000-HV | 125 |
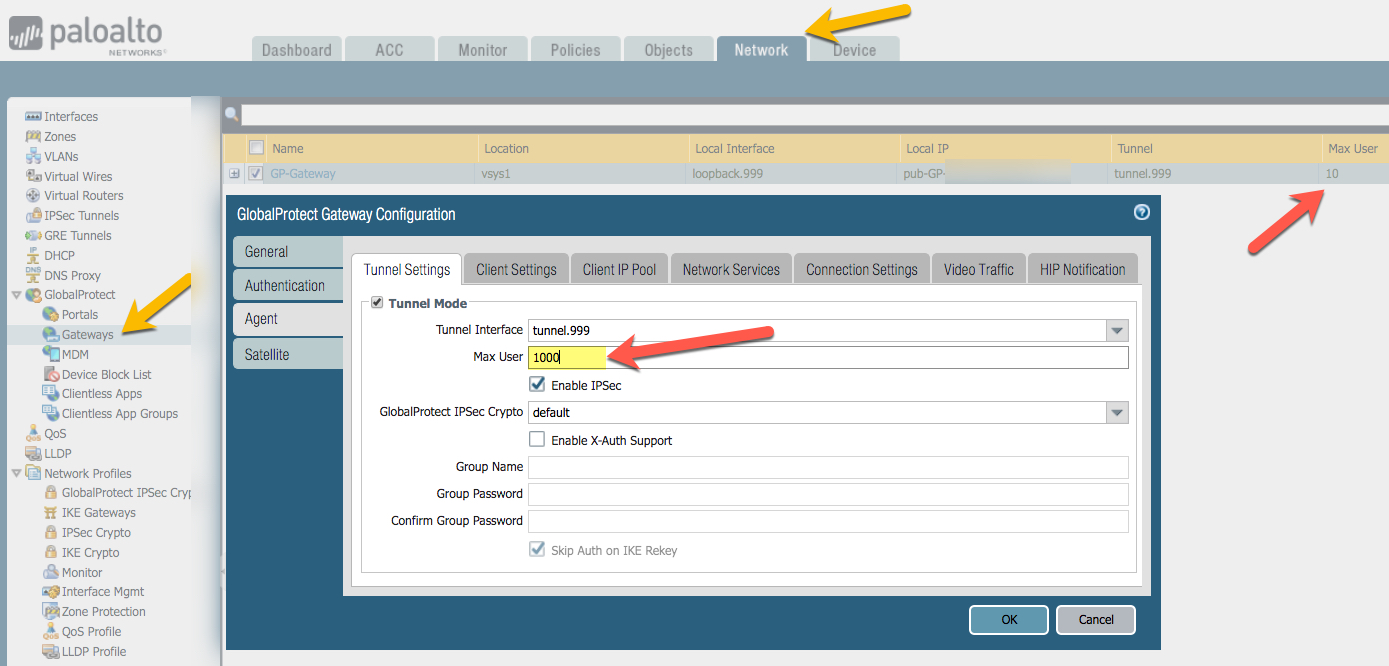
Make sure to alter Max Users on the Agent!
GlobalProtect Clientless VPN
| Firewall Model | Max SSL tunnels |
|---|---|
| PA-5280 | 10,000 |
| PA-5260 | 10,000 |
| PA-5250 | 5,000 |
| PA-5220 | 2,500 |
| PA-3260 | 400 |
| PA-3250 | 400 |
| PA-3220 | 200 |
| PA-850 | 200 |
| PA-820 | 200 |
| PA-460 | 200 |
| PA-450 | 200 |
| PA-440 | 100 |
| PA-220 | 20 |
| VM-700 | 2,500 |
| VM-500 | 1,200 |
| VM-300 | 400 |
| VM-200 | 100 |
| VM-100 | 100 |
| VM-50 | 40 |
| VM-1000-HV | 125 |
NOTE: GP Clientless requires the GP subscription
IPSec VPN
| Firewall Model | IPSec VPN throughput | Max IKE Peers | Site to site (with proxy id) | SD-WAN IPSec tunnels |
|---|---|---|---|---|
| PA-5280 | 27 Gbps | 5,000 | 15,000 | 5,000 |
| PA-5260 | 27 Gbps | 5,000 | 15,000 | 5,000 |
| PA-5250 | 18 Gbps | 4,000 | 12,000 | 4,000 |
| PA-5220 | 10 Gbps | 3,000 | 10,000 | 3,000 |
| PA-3260 | 4.8 Gbps | 3,000 | 6,000 | 3,000 |
| PA-3250 | 3.2 Gbps | 3,000 | 6,000 | 3,000 |
| PA-3220 | 2.7 Gbps | 2,000 | 4,000 | 2,000 |
| PA-850 | 1.6 Gbps | 1,000 | 2,000 | 1,000 |
| PA-820 | 1.2 Gbps | 1,000 | 2,000 | 1,000 |
| PA-220 | 500 Mbps | 1,000 | 1,000 | 1,000 |
| VM-700 | 6 Gbps | 2,000 | 8,000 | 2,000 |
| VM-500 | 4 Gbps | 1,000 | 4,000 | 1,000 |
| VM-300 | 1.8 Gbps | 1,000 | 2,000 | 1,000 |
| VM-200 | 1 Gbps | 1,000 | 1,000 | NA |
| VM-100 | 1 Gbps | 1,000 | 1,000 | NA |
| VM-50 | 100 Mbps | 250 | 250 | NA |
| VM-1000-HV | 1.8 Gbps | 1,000 | 2,000 | NA |
FAQs - Global Protect
What is Palo Alto Networks GlobalProtect?
It is a software agent that extends the protection of a corporate perimeter to remote user laptops thereby applying all the same policies and protections to remote users. This includes URL filtering, threat inspection, visibility, etc. already being provided to local users. It does this by utilizing three components:
1) Existing corporate PAN firewall(s) acting as gateways.
2) A GlobalProtect portal for management including host configuration characteristics. The portal deals with authentication and downloading of new agent software if needed for the client.
3) An agent that communicates to the portal, creates an encrypted session to the gateway(s) and it creates a Host Information Profile (HIP) of the client device.
4) Support for Apple iOS.
1) Existing corporate PAN firewall(s) acting as gateways.
2) A GlobalProtect portal for management including host configuration characteristics. The portal deals with authentication and downloading of new agent software if needed for the client.
3) An agent that communicates to the portal, creates an encrypted session to the gateway(s) and it creates a Host Information Profile (HIP) of the client device.
4) Support for Apple iOS.
What are the benefits?
Consistent policy and central management to apply to local or remote users thereby simplifying policy enforcement without additional hardware or additional management systems.
What platforms does it run on?
The portal management runs on the Palo Alto Networks firewall (High Availability option too).
What do I need [to buy]?
PAN firewalls are used as the enforcement appliances. From a license perspective, a portal license must be purchased for the unit (or more for redundancy) doing the portal management. Licenses for GlobalProtect are required on all desired PAN units acting as gateways (this does not have to be all the deployed PANs, just those desired as remote access gateways). Support is purchased for updates to the software along with technical support.
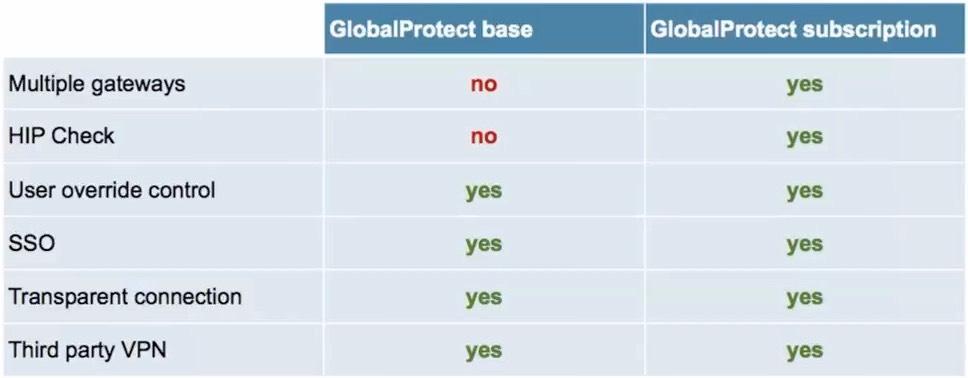
GP (Global Protect) is included in a lite basic form which supports a single gateway and portal (without the host endpoint enforcement). To enable multiple gateways and/or endpoint enforcement, and/or mobile support, optional licenses purchases and subscriptions are required.
GP (Global Protect) is included in a lite basic form which supports a single gateway and portal (without the host endpoint enforcement). To enable multiple gateways and/or endpoint enforcement, and/or mobile support, optional licenses purchases and subscriptions are required.

NOTE: Starting with PANOS 7.0, you no longer need to purchase the GP Portal License.!
What about split tunneling?
Yes, split tunneling policies can be defined via the portal management system.
NOTE: The behavior does change starting with PANOS 7.0, please read the release notes to better understand the changes.
NOTE: The behavior does change starting with PANOS 7.0, please read the release notes to better understand the changes.
How does it compare to SSL VPN?
SSL VPN connectivity via a lite version of GP is already included on the PAN base systems to address remote access for users. GlobalProtect license option extends this further by automatically selecting the closest gateway, making sure remote users get the same policies applied by keeping them connected to the gateways enforcing the policies and making sure that hosts comply with configuration requirements.
GlobalProtect acts as a transparent SSL VPN regardless of how users connect to the Internet and making sure those connections remain encrypted. GP will use IPSec by default for performance benefits, but can fallback to SSL where networks disallow IPSec traffic.
GlobalProtect acts as a transparent SSL VPN regardless of how users connect to the Internet and making sure those connections remain encrypted. GP will use IPSec by default for performance benefits, but can fallback to SSL where networks disallow IPSec traffic.
What kind of host characteristics can be checked via HIP (Host Information Profiles)?
- Operating system and patch level
- Host anti-malware version
- Host firewall version
- Disk encryption
- Data backup products
- Customized host conditions
NOTE: Above are enabled via HIP profiles on the portal and require optional Global Protect license(s).
- Host anti-malware version
- Host firewall version
- Disk encryption
- Data backup products
- Customized host conditions
NOTE: Above are enabled via HIP profiles on the portal and require optional Global Protect license(s).
Are all users placed in the same internal network/zone?
You can control where users are placed in terms of a security zone. Users can be placed in the same internal network (typically Trust) zone or they can have their tunnels terminated in a different secure zone (e.g. RemoteUsers) and then use security policies tied to usernames and/or applications to control and restrict access. This includes threat inspection features, spyware, malware, ant-virus, etc. Sounds like a great idea, right?
How/Can I remove Global Protect from my computer/laptop?
It can be done, but you need to talk with your PAN administrator and have them check the Palo Alto Networks support site. We're not going to help IT users remove a corporate control from their desktops except via the official corporate administrators. Yes, GP is an excellent tool for enforcing corporate policies and as such should not be easy to disable or remove by unauthorized users.
If you would like us to work with the IT department, we are available for Professional Services via a billable engagement.
If you would like us to work with the IT department, we are available for Professional Services via a billable engagement.
What are common trouble shooting commands and debug commands for Global Protect?
show log system direction equal backward subtype equal globalprotect
show global-protect-gateway flow
show global-protect-gateway flow tunnel-id
show global-protect-gateway current-user
show global-protect-gateway gateway name
show user ip-user-mapping
show user ip-user-mapping type GP
show user ip-user-mapping ip
debug device-server dump hip-profile-database
debug device-server dump hip-report computer user ip
tail follow yes mp0log devsrv-log
tail follow yes mp-log authd.log
show global-protect-gateway flow
show global-protect-gateway flow tunnel-id
show global-protect-gateway current-user
show global-protect-gateway gateway name
show user ip-user-mapping
show user ip-user-mapping type GP
show user ip-user-mapping ip
debug device-server dump hip-profile-database
debug device-server dump hip-report computer
tail follow yes mp0log devsrv-log
tail follow yes mp-log authd.log
Any specifications listed are informational only. Please consult product manufacturer data sheets. Values are subject to changes due to firmware releases, traffic mix changes, typos and unique circumstances.
About Us | Contact Us | Privacy Policy | EOL
© 2023 Altaware, Inc. | All rights reserved.
949-468-0020
CYBER SECURITY skills in ORANGE COUNTY, CA
Remote cyber security skills/services within the USA